Special Report: Privacy in the Data-Driven Enterprise
An entire week of coverage devoted to the question: How do we give privacy back to the people when customer data is now the coin of the realm and the fuel that powers business?
December 9, 2022
Since the dawn of the dot-com era, more and more business models have come to rely on convincing customers that there is indeed such a thing as a free lunch.
Wise people know that isn't true. "Free" nowadays just means you don't pay with your money; you pay with your life. At least, that is, some of the details about yourself, your life, and your behavior, so that the data can be collected, analyzed, bought, sold, squeezed for intelligence, shaken for loose change, (stolen by cyberattackers), and fed into ever-more sophisticated technology to motor "data-driven" business initiatives. This isn't necessarily sinister; organizations may use personal data on customers to provide better service, more customized healthcare. And for some industries, trading data is the main way to sustain themselves, as people get out of the habit of spending actual money on things like music and news. Businesses are required to maintain some personal data on employees and may monitor those employees' behavior to improve productivity, and also worker safety, or employee wellness. Data is so helpful, that businesses collect it about everything.
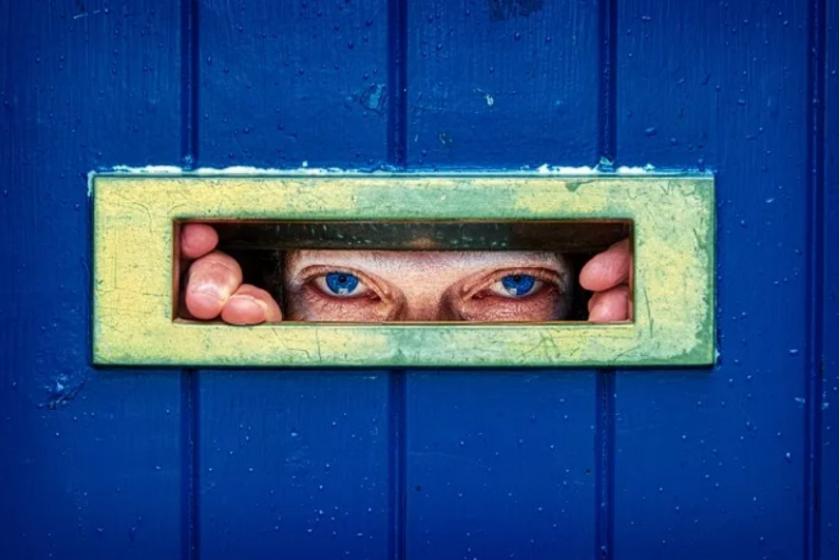
The end result is a culture of surveillance.
Even when well-intentioned, data collection can be very dangerous -- both to the individual and to the business taking stewardship of it.
Consumers and employees alike are waking up to these realities and want their privacy back; regulators are stepping in with tighter oversight and steeper punishments. And many forward-thinking organizations and innovative IT leaders are taking privacy rights seriously, recognizing that protecting the privacy of their consumers and employees is an important part of maintaining their trust.
But where to start?
A look at most organizations' data stores would show a messy, tangle of poorly governed datasets growing out of control. Lots of the data your organization collects it probably doesn't need, never uses, doesn't even know that it has. It's eating up storage space, and is an accident waiting to happen. An appetizing target for a cyberattacker; a costly violation for a regulatory auditor; an uncomfortable situation when law enforcement brings a discovery request; a public relations embarrassment that causes the organization to lose the trust of customers or employees. All of the above, or worse.
Read the rest of this article on InformationWeek.
Other articles in the series:
Data Privacy and Protection in the Age of Cloud: With more data on more cloud platforms being subject to increasingly stringent regulations, traditional approaches to protecting data fall short.
Privacy Debate for 2023: Can Data Collection Persist As Is?: More layers of state and federal regulation on data privacy loom on the horizon, with political agendas and business needs also adding tension to the mix.
Trusted Execution Environments Make Computing More Private: Trusted execution environments are changing the face of cloud computing -- and they will have an even bigger impact in the months and years ahead.
Data Strategy: Synthetic Data and Other Tech for AI's Next Phase: Forrester's Data Strategy & Insights event will offer insights to help you take your machine learning and artificial intelligence initiatives to the next phase.
Stealth Data Collection Threatens Employee Privacy: Secretly and quietly, often without enterprise knowledge or permission, cybersecurity and monitoring tools are scooping up an array of sensitive employee data.
How Should Data Brokers and Credit Bureaus Be Protecting Your Data?: The largest stewards of personally identifiable information have poor cybersecurity records. What have they learned from previous breaches?
Data Clean Rooms: Enabling Analytics, Protecting Privacy: Data clean rooms offer a way for organizations to collaborate with and share data in a protected environment that preserves privacy and governance. Here's why they are on the rise now.
The Top 5 Data Privacy Penalties Post-GDPR: From California to China and the country that fined itself, here are the five most interesting data privacy penalties of 2021-22.
How to Build Privacy By Design Into Customer Experience: The predatory nature of data collection is spiking demand for data privacy protection as part of the customer experience. Are you ready to deliver that?
Exploring End-to-End Encrypted Messaging and the Enterprise: Data clean rooms offer a way for organizations to collaborate with and share data in a protected environment that preserves privacy and governance. Here's why they are on the rise now.
The Companies Leading Privacy-Enabling Tech: Selecting a data privacy management vendor requires organizations to carefully consider their specific needs, and the level of help they need to meet compliance requirements.
What Do the Multimillion-Dollar Google Settlement, Meta Fine Mean for Data Privacy?: Google agreed to pay a significant amount in a settlement for violating consumer privacy laws. Could this settlement and Meta’s latest fine be the beginning of a new future for data privacy?
About the Author(s)
You May Also Like





