Introduction to Infrastructure as Code
Small misconfigured settings plague many IT environments, impacting security and stability. Infrastructure as code lets you apply a consistent configuration to a broad range of endpoints.
August 30, 2018

Infrastructure as code (IaC) is the practice of configuring infrastructure using code instead of using a UI (user interface) or CLI (command line interface). Configuration settings are written within configuration files and then applied.
At the highest level, configuration files are written to describe the desired state of a system. The configuration is applied against target systems, usually performed with a configuration manager such as Ansible or Terraform.
IaC can help solve common infrastructure management problems such as:
Inconsistent configuration
Out of date documentation
Configuration change tracking
Configuration drift detecti
The syntax for writing a described state is provided by the configuration manager using a language known as a Described State Language or DSL. A DSL doesn’t require all the steps to apply the state, only the desired configuration values.
In plain language, it would be the equivalent of a tech lead telling an engineer to allow SSH to a group of servers from any external IP address. The tech lead cares more about achieving the desired outcome than the steps involved.
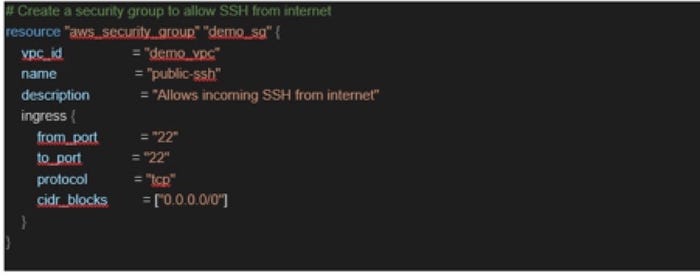
The below snippet is from a Terraform workflow when applied it will create a security group in AWS to allow SSH access from any IP address.
config-brett.jpg
The configuration shown describes the desired state of the security group demo_vpc. It does not specify the steps to make it happen.
Applying consistent configuration to a large range of endpoints is one of the significant value propositions of IaC. Small misconfigured settings plague many IT environments, impacting security and stability.
For example, the configuration of a Syslog setting is typically the same for many network devices in the same location. If this needed to be updated manually, the process would be time-consuming and prone to mistyping of the new address. Using IaC, the configuration file is updated and applied to those networking devices.
If the Syslog server address is incorrect in the configuration file, the setting on the devices will be consistently wrong; which is easier to spot and resolve than 5 percent of devices not functioning.
As-Built documentation is meant to assist with the rebuilding of a system or setting validation. The document is almost always out of date by the time it goes from draft to final release. By using IaC, the configuration file becomes the as-built document.
The goal is to specify as many configuration settings as possible within the configuration file. This makes the configuration file a single source of truth for the current environmental state.
A configuration file does not replace design or deployment step documentation, as it only states the desired state not the rationale behind the setting. Specifying system configuration in text files enables the use of version control platforms to track changes. With good version control practices, this ensures that all changes to the environment are committed to version control before they are applied.
Changes in text files are much easier to track compared to an accidental option selection within a user interface, a missed step within a list of tasks.
Managing change
When working with IaC, it is crucial to understand the impact of the change. Some settings require services to be restarted to apply fully. If you run a configuration against all your web servers and restart the service, you might take the entire site offline.
I mentally break the task into two separate parts set and apply. This helps me understand the impact and process. Conversationally, this is still just referred to as applying a configuration.
Set is merely the changing of the setting, such as updating of a configuration file on the server. Just because a setting changes, doesn’t mean that it’s part of the running config.
Apply is the process of getting the setting into the running configuration. This could be immediate at the time of setting change, or it might require a service restart. Sometimes the service needs to be stopped before setting change and started after. Understanding the requirements for applying the setting helps determine the overall process.
Configuration managers are commonly used to apply the desired configuration, providing a framework for managing infrastructure configuration.
There are many configuration managers, each with their own pros and cons. The right one for you depends on your specific circumstances. One tool might be better for networking devices, while another is stronger for server OS configuration.
Before selecting a configuration manager, assess the problem that you want to solve and the characteristics of the system on which the settings will be applied.
Adoption of IaC can help tackle many system management problems, especially when it comes to configuration consistency.
About the Author
You May Also Like




