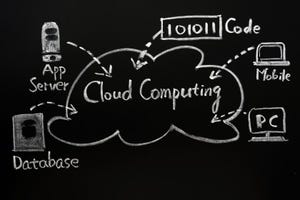
Cloud Networking
Cloud networking is the use of cloud computing technologies and services to optimize and manage network infrastructure and resources.
Complexity cycle
Network Infrastructure
The Complexity Cycle: Infrastructure Sprawl is a KillerThe Complexity Cycle: Infrastructure Sprawl is a Killer
Standardizing with a platform approach is the way to put the brakes on the complexity cycle. You can’t stop the cycle completely. But you can slow it down so it doesn’t overwhelm you.
SUBSCRIBE TO OUR NEWSLETTER
Stay informed! Sign up to get expert advice and insight delivered direct to your inbox