Understanding IPv6: Solicited-Node Multicast In Action
In the last installment of her IPv6 series, Denise Fishburne explains how to find the MAC address associated with a Layer 3 IPv6 address.
November 11, 2014

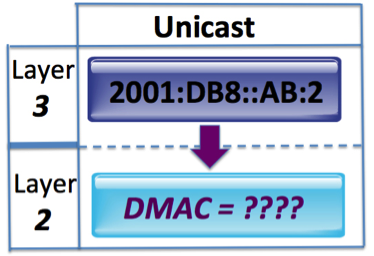
The last few blogs in my series on IPv6 have focused on solicited-node multicast, which provides the functionality for Neighbor Discovery in IPv6 addressing. We ended the last blog with a cliffhanger, asking, "In IPv6, how do we find the Layer 2 MAC address associated with a Layer 3 IPv6 address?"
Time to put the pieces together
In this series of blogs, I have laid out all the varying puzzle pieces needed to answer this question. Let's start putting those puzzle pieces together.

In this blog, we learned that, if a device has an IPv6 global address of 2001:DB8::AB:1/64, then, according to RFC 4291, it must also "compute and join" the IPv6 solicited-node multicast address FF02::1:FFAB:1.
By the same logic, that means the node associated with the IPv6 address of 2001:DB8::AB:2 must "compute and join" the IPv6 solicited-node multicast address FF02::1:FFAB:2.
So our first puzzle piece gets us to here:
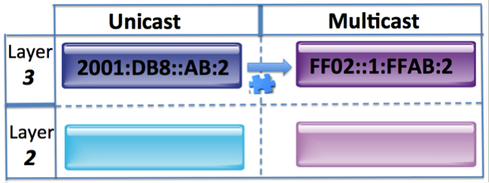
But so what? How does that get us any closer to getting the DMAC associated with Router B's IPv6 global unicast address? All it did was give us a multicast address that this IPv6 unicast address must join.
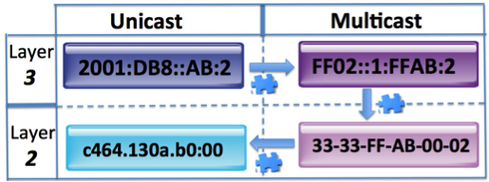
Let's add another piece of the puzzle. From this blog, we learned that 33-33-00-00-00-00 to 33-33-FF-FF-FF-FF are reserved as the destination MAC address for all IPv6 multicast.
So our second puzzle piece gets us to here:
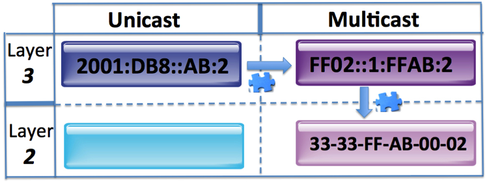
But still, how far have we really come? Let's add another puzzle piece.
Remember that, with IPv4, though Router A did not know the Layer 2 destination MAC address of Router B's IPv4 address 10.10.10.2, Router A did know of a Layer 2 MAC address that Router B was "listening in" on. This was Layer 2 broadcast address FF:FF:FF:FF:FF:FF. With this knowledge, Router A can "reach out" via a Layer 2 broadcast "shout out" and ask Router B about its MAC address that is associated with IP address 10.10.10.2.
Of course, Router B would not be the only device to see this "shout out" to the broadcast Layer 2 MAC address FF:FF:FF:FF:FF:FF. Every other node on that IPv4 broadcast domain would, as well.
So, because Router A knows of a Layer 2 MAC address that Router B is "listening in" on, Router A can communicate to Router B and ask for its unicast MAC address associated with its unicast IP address.
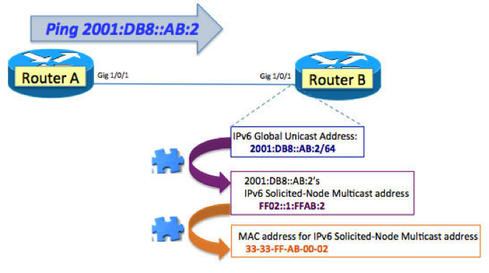
Though there is no broadcast in IPv6, our puzzle pieces above come together to give Router A a Layer 2 MAC address that Router B must be "listening in" on: 33-33-FF-AB-00-02.
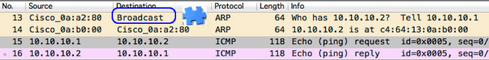
Because Router A knows of a Layer 2 MAC address that Router B is "listening in" on, Router A can communicate to Router B and ask what its unicast MAC address is that is associated with its unicast IPv6 address. In IPv6, this is known as Neighbor Discovery. Let's sniff the wire.
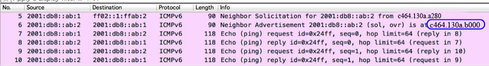
Note the details:
Line 5: Neighbor Solicitation for IPv6 address 2001:DB8::AB:2
Source MAC: c464.130a.a280 (Router A)
Destination IPv6 Solicited-node multicast address FF02::1:FFAB:2
Destination MAC: 33-33-FF-AB-00-02
Line 6: Neighbor Advertisement from Router B that it has IPv6 unicast address 2001:DB8::AB:2 and MAC address of c464.130a.b000
Line 7: Router A now finally has the DMAC for Router B's IPv6 unicast address and can send the ICMPv6 echo request to Router B.
The MAC address is discovered. I hope you have enjoyed this series as much as I have enjoyed writing it. Happy IPv6-ing.
About the Author(s)
How to Amplify DevOps with DevSecOps
May 22, 2024Generative AI: Use Cases and Risks in 2024
May 29, 2024Smart Service Management
June 4, 2024

